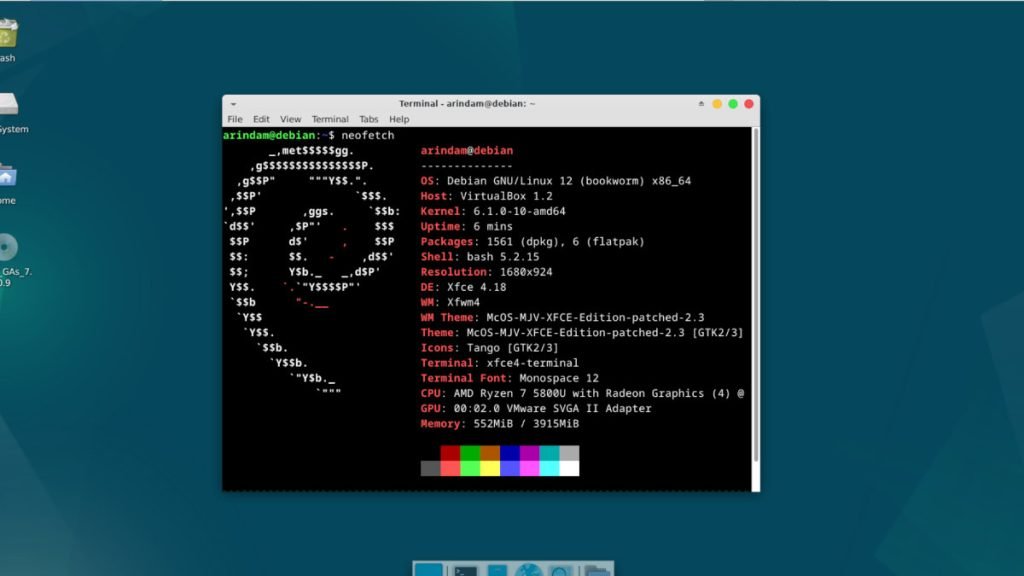
The first point release – Debian 12.1 “Bookworm”, is now available. Upgrade now.
The Debian project has unveiled the first update to its stable distribution, Debian 12 “bookworm,” with a focus on addressing security issues and resolving critical bugs. This point release delivers a much-needed boost to the overall stability and reliability of the operating system.
The primary highlight of Debian 12.1 is the extensive set of corrections and enhancements aimed at fortifying the system’s security. Numerous security advisories have been released alongside this update, providing users with detailed information on the addressed vulnerabilities.
It’s important to clarify that Debian 12.1 is not an entirely new operating system version; instead, it serves as an update that applies fixes and improvements to existing packages. This means that users need not discard their current Debian 12 installations; rather, they can upgrade their packages to the latest versions using an up-to-date Debian mirror.
For users who frequently update their systems through security.debian.org, the transition to Debian 12.1 should be relatively smooth, as many of the essential security updates have already been incorporated into this point release.
The release addresses a wide range of packages, ensuring comprehensive coverage of security and functionality issues. Some of the notable packages receiving attention include:
- aide: Proper handling of system user creation and child directory processing improvements.
- cups: Fixes for use-after-free and heap buffer overflow vulnerabilities.
- dbus: New upstream stable release with fixes for denial of service issues.
- glibc: Several fixes, including buffer overflow in gmon and deadlock in getaddrinfo.
- node-undici: Security fixes to protect against Host HTTP header injection and potential ReDoS on Headers.set and Headers.append.
- qemu: A new stable release with fixes for various issues, including preventing the opening of special files.
- sudo: Corrected event log format for improved functionality.
- systemd: A new bugfix release addressing various issues.
These are just a few examples, as the release covers an extensive list of packages, providing a robust and secure foundation for Debian users.
Additionally, Debian 12.1 introduces some adjustments to address serious problems identified in the previous version, ensuring an optimized user experience and improved performance.
While this update brings several enhancements, it is crucial for users to promptly apply the patches to bolster the security of their systems. With cyber threats becoming increasingly sophisticated, timely updates are essential in safeguarding against potential exploits.
As with any major release, the Debian community remains committed to providing ongoing support, addressing issues, and releasing further updates as needed to ensure the stability and security of the distribution.
Users can obtain Debian 12.1 through official Debian mirrors or by upgrading their existing Debian 12 installations. Keeping systems up-to-date is paramount in maintaining a secure and reliable computing environment, and the Debian 12.1 release marks a significant step forward in this regard.
To update your existing Debian 12 “Bookworm”, simply run the following commands from the terminal:
sudo apt update && sudo apt upgrade -y
For fresh ISO download, visit the below pages:
In conclusion, Debian 12.1 serves as a testament to the Debian project’s dedication to delivering a rock-solid and secure operating system. With a comprehensive array of bug fixes and security enhancements, Debian users can continue to rely on this versatile distribution for all their computing needs.
Note: The Debian 12.1 update is now available for download. Users are strongly encouraged to upgrade their systems to benefit from the security and functionality improvements this release offers.
Via official release announcement
Recent articles from DebugPoint.com
- 10 Things to do After Installing Fedora 44 (Workstation)on May 10, 2026
- Upgrade to Fedora 44 from Fedora 43 Workstation (GUI and CLI)on May 9, 2026
- Future of AI in Ubuntu: Thoughtful Integration via Snapon May 2, 2026
- Xubuntu 26.04 LTS: Best New Featureson April 30, 2026
- Fedora 44: Best New Featureson April 30, 2026